One of the most sophisticated types of attacks that threaten our digital landscape is Cross-Site Request Forgery (CSRF). According to the Open Web Application Security Project (OWASP), CSRF vulnerabilities are among the top 10 most critical web...
In many applications including surfing the internet, chatting, sending confidential documents anonymity has become a necessary and legitimate desire. A piece of information can be encrypted by using many encryption techniques...
The Nemesis Project is designed to be a command line based, portable human IP stack for UNIX-like and Windows systems. The suite is broken down by protocol, and should allow for useful scripting of injected packets from simple shell scripts...
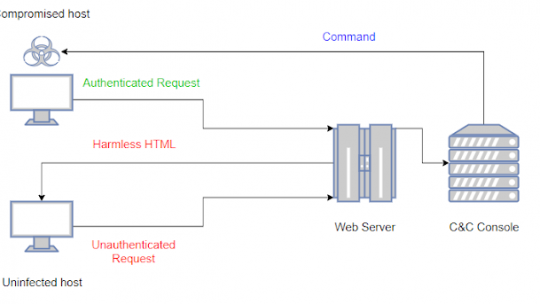
LOLBITS is a C# reverse shell that uses Microsoft’s Background Intelligent Transfer Service (BITS) to communicate with the Command and Control backend. The Command and Control backend is hidden behind an apparently harmless flask web...
Companies selling “security scorecards” are on the rise, and have started to become a factor in enterprise sales. We have heard from customers who were concerned about purchasing from suppliers who had been given poor ratings, and...
Fail2Ban is an intrusion prevention framework written in Python that protects Linux systems and servers from brute-force attacks. We can setup Fail2Ban to provide brute-force protection for SSH on our server, this will ensure that the server...
ReconCobra Reconcobra is Foot printing software for Ultimate Information Gathering Kali, Parrot OS, Black Arch, Termux, Android Led TV Interface Software have 82 Options with full automation with powerful information gathering capability...